How to Monitor Traffic on Managed Servers
All Managed Servers include a set monthly traffic quota of 10 TB. We monitor all accounts and you are billed for each GB of traffic that exceeds the monthly quota on a South African server. German servers offer unlimited traffic, with a bandwidth restriction at 30 TB.
Traffic monitoring
Your konsoleH control panel makes it possible for you to monitor your traffic usage on a regular basis. You can view server traffic statistics and filter these according to various billing periods. A traffic report is generated according to the selected report type and specified time period.
It is important that you regularly use this tool to check for any unusual traffic activity.
Traffic Reports
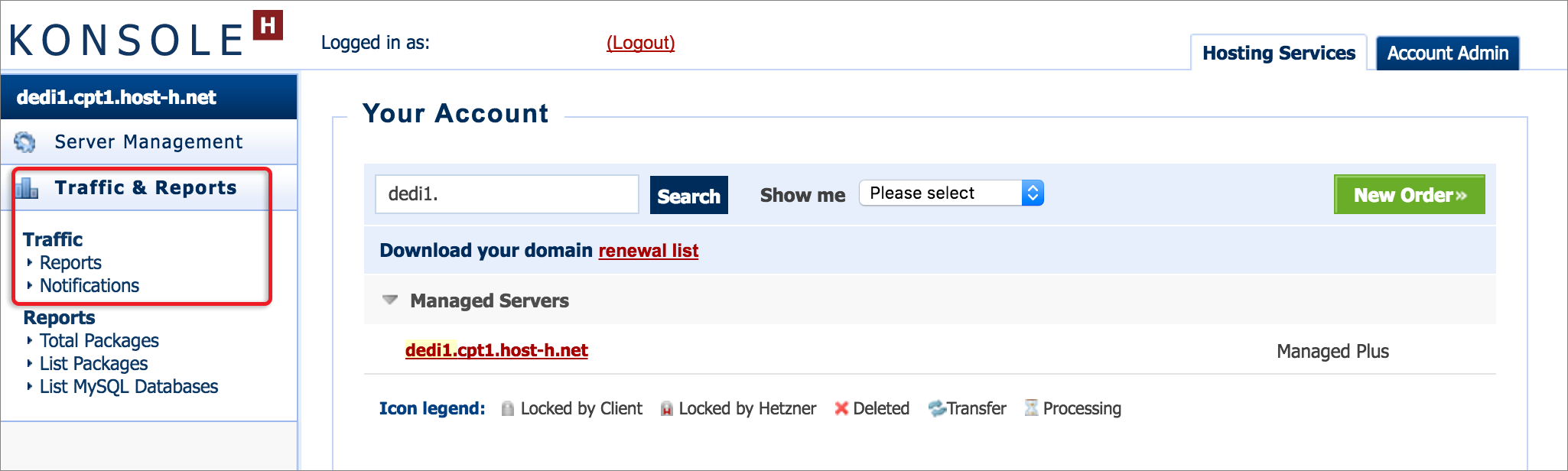
- Browse to konsoleH and log in at Admin level
- Select or search for a server name in the Hosting Services tab
- Select Traffic & Reports

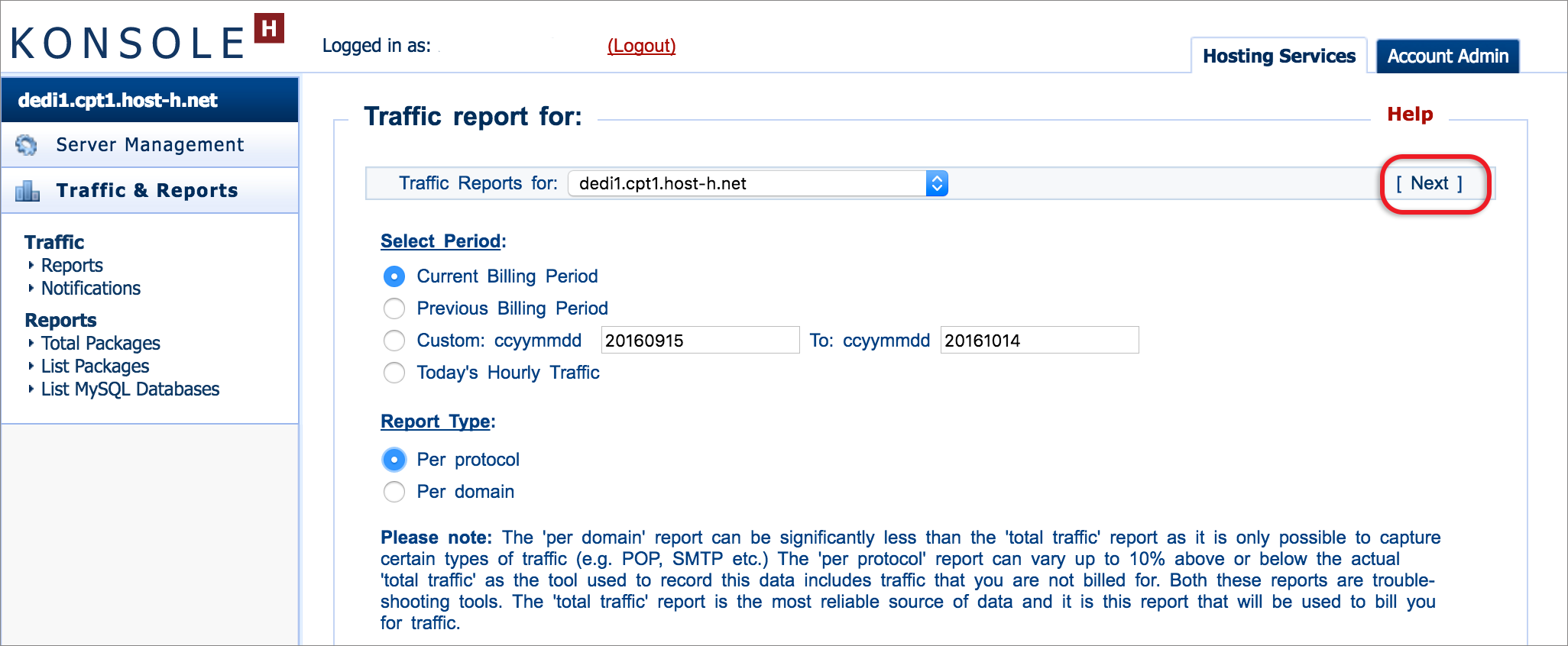
- Adjust the Display options and Report Type as required > Next

- A table displaying the traffic will be displayed. The dates can be adjusted as required, then select Next.
Traffic Reporting:
-
Total Traffic
Displays the total traffic as well as incoming and outgoing requests generated by one IP address over your specified time period. Over-usage charges generated are clearly displayed on the graph. The information recorded in the ‘total traffic’ report is what is used for billing purposes as it includes all protocols and means of access, as logged by the router serving the data centre.
-
Per Protocol
Displays a breakdown of traffic, incoming and outgoing requests, per protocol (HTTP, HTTPS, SMTP, POP, MySQL, SSH and other) generated by the server over your specified period.
-
Per Domain
Displays a breakdown of traffic generated per domain over your selected period. Traffic that is not generally ascribed to a particular domain includes spam mail that is intercepted by the spam checker, mail sending or deliveries that fail during the transaction and need to be resent and mail download attempts that are interrupted.
Only certain traffic types are logged in a manner that associates their use with a specific domain. These include WWW/HTTP, POP3, SMTP, and FTP. Additional traffic that is not accounted for under the ‘per domain’ report, but contributes to the ‘total traffic’ report, is detailed under ‘per protocol’ traffic report.
Traffic Notifications:
In order to assist you in effectively monitoring your traffic usage, we have set up a notification system in konsoleH to forewarn you of over-usage.
-
Quota threshold
There is a default threshold built into the system which is 20% below your allocated traffic quota (i.e. the percentage threshold will be set to 80%). Should your traffic usage either reach or exceed the default threshold, konsoleH will send a daily notification email to inform you that the threshold has been reached and that there is a possibility of your server exceeding the traffic quota.
You have the option to adjust your threshold as well as the frequency of these notifications.
-
Burst threshold
You have the option to be notified when your server exceeds a certain amount of traffic (which you determine) within a period of time that you specify. For example, if you’d like to be notified when you have used more than 500 MB of traffic within 3 hours, simply set your burst threshold to these values and konsoleH will send you a notification email, should this threshold be reached. A default notification is enabled which is set to 200 MB in 1 hour.
Excessive traffic generated due to internet abuse
We take responsibility for the operating system and the applications we have deployed on a Managed server. However, we have limited control over applications that can be adjusted by clients to suit their individual needs. These adjustments could entail website content and scripts, applications or utilities running on the server. For example, a site running a third party script where a vulnerability exists may be exploited to upload content or generate mass mail.
Traffic, as described above, remains the responsibility of the customer.
Our System Administrators receive hourly notifications, reporting on high traffic volumes on Managed servers. A modest threshold is set and excessive activity investigated. As such, customers are informed timeously before extreme charges are accumulated. However, we can’t guarantee that all malicious activity of this nature will be detected before cost implications occur.